Over the past couple of years, HTTPS has been a common topic in the tech news. The rate of change to keep pace with best practice has ramped right up - fueled by a push from many tech giants to rid the internet of unencrypted or weakly encrypted communications over the internet. I’d go as far as to say that 2016 has been “the year of HTTPS” - with game changing moves setting the tone for further changes in 2017. Are you keeping pace with these changes? Are you ready for more?
Google’s stance on HTTPS being a top priority has been pretty clear for some time now - back in 2014, they made a change to their ranking algorithms for Search to include HTTPS as a positive indicator. This was a bit of a controversial move at the time, as it added overhead for administration, and additional costs for small website operators.
2016 has brought a disruptive change to HTTPS through the “Let’s Encrypt” project. Traditionally, to obtain an HTTPS certificate for your site, you’d need to purchase one through a certificate vendor. This would be a manual process, and would need to be repeated whenever the certificate expired. This project has taken a different stance - and offers HTTPS certificates to anyone for free. Backed by some huge industry players (including Google, Cisco, Facebook and HP, among many others), they’ve established a fully automated approach for provisioning certificates. By making the process free and easy, they’ve made HTTPS accessible to everyone.
It’s no surprise then that 2016 has seen massive growth in HTTPS adoption - by some reports the rate of HTTPS adoption has doubled this year. Increased awareness of information gathering by governments, and a general growth of interest in cyber security, combined with better access to certificates has given HTTPS the boost it needed.
With 2017 ahead - more changes are afoot. Browser vendors are pushing hard for HTTPS as a requirement on new technologies. Any new app released to the Apple App Store will need to implement strong cryptography. Google Chrome will begin marking non-HTTPS sites as “insecure”.
For many new features being rolled out to web browsers, they’re being implemented with a requirement for the site using the feature to be accessible via HTTPS websites exclusively. This is another push from browser vendors to get all sites across: If you want the new features, you need to be on HTTPS.
During 2017, it’s expected that Apple will be requiring not just HTTPS - but strong HTTPS - for any content accessible within iOS apps. This was previously set for January 1 - but Apple have backed down from this date, and have not yet set a new date for the switchover. This would be a very hard line move from Apple - but it’s in line with their ongoing commitment to their user’s security and privacy. The requirements from Apple are the strictest we’ve seen at this stage - the “strong” HTTPS being referred to here includes ensuring that HTTPS is configured with the appropriate algorithms for “Forward Secrecy” - ensuring that even if a single message is decoded, that other messages are not also vulnerable.
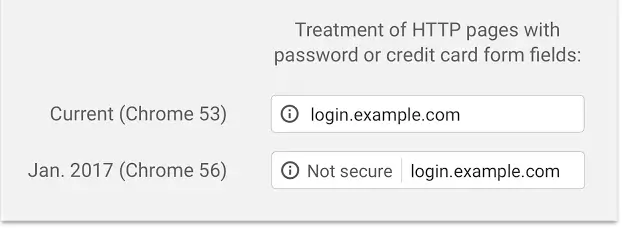
From Google Chrome version 56 (expected to land in January 2017) any sites which allow users to log in, or collect credit card details, will be marked as “Not Secure” - and they’ve indicated that they will continue to ramp this up, showing even more HTTP sites as “Not Secure” going forward.
So how can you know if you’re ready?
You can run a quick check on your domains using Qualys’ SSL Labs - which will give you a letter-grade rating. You’re looking to get an “A” grade. The scan can take a few minutes to run, but will perform a deep analysis on your HTTPS Configuration.
If you’re already getting an A grade on your sites - well done!
If you’re getting anything less - it’s time for an upgrade. Some issues can be resolved by changing configuration on the web server, others may require a certificate to be re-issued from your existing provider. If you plain don’t have a certificate - 2017 is the year to pick one up - either from Let’s Encrypt or another provider.